Redshift
Configuring your Redshift destination.
Prerequisites
- If your Redshift security posture requires IP whitelisting, have the data syncing service's static IP available during the following steps. It will be required in Step 2.
- By default, Redshift authentication uses role-based access. You will need the trust policy prepopulated with the data-syncing service's identifier to grant access. It should look similar to the following JSON object with a proper service account identifier:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"sts:AssumeRoleWithWebIdentity"
],
"Principal": {
"Federated": "accounts.google.com"
},
"Condition": {
"StringEquals": {
"accounts.google.com:oaud": "<some_organization_identifier>",
"accounts.google.com:sub": "<some_service_account_identifier>"
}
}
}
]
}
Network allowlistingCloud Hosted (US):
35.192.85.117/32Cloud Hosted (EU):
104.199.49.149/32If private-cloud or self-hosted, contact support for the static egress IP.
Step 1: Create a Limited User in Redshift
- Connect to Redshift using the SQL client.
- Execute the following query to create a user to write the data (replace
<password>with a password of your choice).
CREATE USER <username> PASSWORD '<password>';
Creating a user without a password.Role based auth does not require a password. You may create the user using
CREATE USER <username> PASSWORD DISABLE;.
- Grant user
createandtemporaryprivileges on the database.createallows the service to create new schemas andtemporaryallows the service to create temporary tables.
GRANT CREATE, TEMPORARY ON DATABASE <database> TO <username>;
The schema will be created during the first syncThe schema name supplied as part of Step 4 will be created during the first connection. It does not need to be created manually in the destination ahead of time.
If theschemaalready existsBy default, the service creates a new schema based on the destination configuration. If you prefer to create the schema yourself before connecting the destination, you must ensure that the writer user has the proper permissions on the schema, using
GRANT ALL ON schema <schema> TO <username>;Once you've provided the
GRANT ALLpermission on the schema, you can safely remove theCREATEpermission on the database (but you must retain theTEMPORARYpermission on the database).
Step 2: Whitelist connection
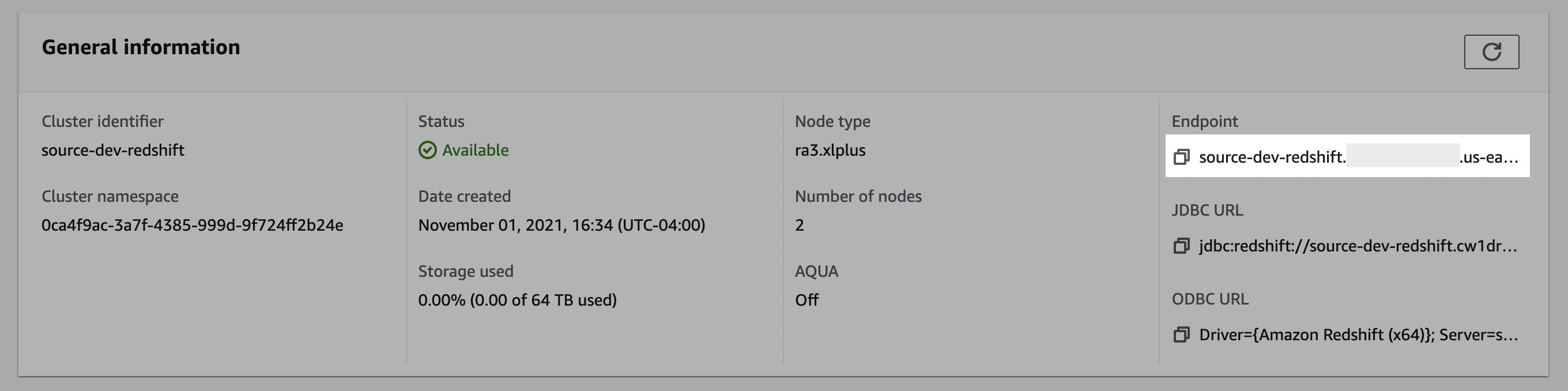
- In the Redshift console, click Clusters, and make a note of the cluster name.
- Select the cluster you would like to connect.
- In the General information pane, make note of the Endpoint details. You may need to use the copy icon to copy the full details to discover the full endpoint and port number.
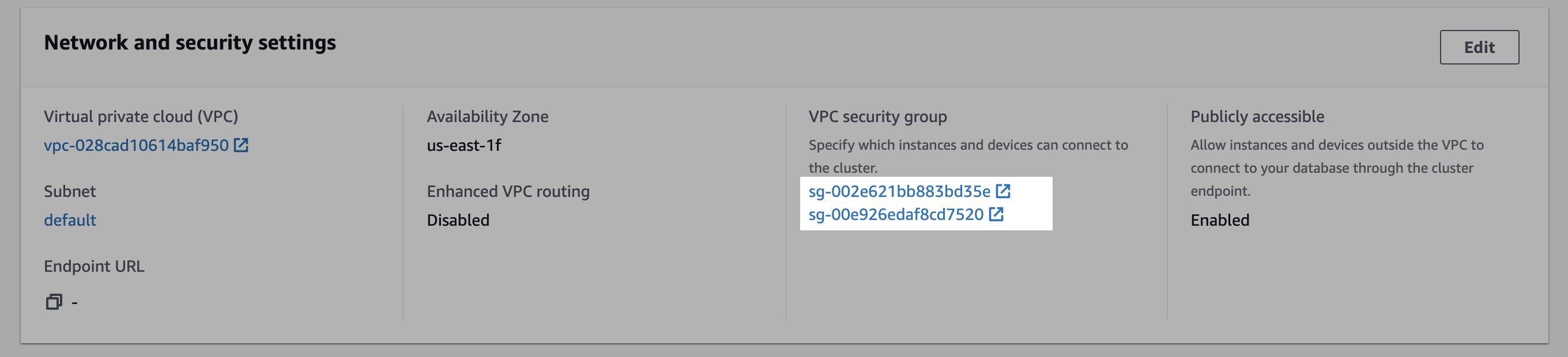
- Click the Properties tab.
- Scroll down to the Network and security settings section.
- In the VPC security group field, select a security group to open it.
- In the Security Groups window, click Inbound rules.
- Click Edit inbound rules.
- In the Edit the Inbound rules window, follow the steps below to create custom TCP rules for the static IP:
a. Select Custom TCP in the drop-down menu.
b. Enter your Redshift port number. (likely
5439) c. Enter the static IP. d. Click Add rule.
Public accessibility and subnet requirementsFor IP allowlisting from outside your VPC, the Redshift cluster must be set to Publicly accessible and deployed in a public subnet with a route to an Internet Gateway. For private Redshift clusters, SSH tunneling is supported. Contact the team for instruction on configuring an SSH tunnel for your Redshift cluster.
Step 3: Create a staging bucket
Create staging bucket
- Navigate to the S3 service page.
- Click Create bucket.
- Enter a Bucket name and modify any of the default settings as desired. Note: Object Ownership can be set to "ACLs disabled" and Block Public Access settings for this bucket can be set to "Block all public access" as recommended by AWS. Make note of the Bucket name and AWS Region.
- Click Create bucket.
Create policy
- Navigate to the IAM service page, click on the Policies navigation tab, and click Create policy.
- Click the JSON tab, and paste the following policy, being sure to replace
BUCKET_NAMEwith the name of the bucket chosen above, and REGION_NAME, ACCOUNT_ID, CLUSTER_NAME, USERNAME, and DATABASE_NAME with the proper Redshift values.- Note: the first bucket permission in the list applies to
BUCKET_NAMEwhereas the second permission applies only to the bucket's contents —BUCKET_NAME/*— an important distinction.
- Note: the first bucket permission in the list applies to
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "s3:ListBucket",
"Resource": "arn:aws:s3:::BUCKET_NAME"
},
{
"Effect": "Allow",
"Action": [
"s3:PutObject",
"s3:GetObject",
"s3:DeleteObject"
],
"Resource": "arn:aws:s3:::BUCKET_NAME/*"
},
{
"Effect": "Allow",
"Action": "redshift:GetClusterCredentials",
"Resource": [
"arn:aws:redshift:REGION_NAME:ACCOUNT_ID:dbuser:CLUSTER_NAME/USERNAME",
"arn:aws:redshift:REGION_NAME:ACCOUNT_ID:dbname:CLUSTER_NAME/DATABASE_NAME"
]
}
]
}
KMS encryption (optional)If your S3 staging bucket uses KMS encryption (CMK), add the following statement to the
Statementarray of your IAM policy to allow data encryption/decryption with your KMS key. Encryption with SSE-C is not currently supported.{ "Effect": "Allow", "Action": [ "kms:GenerateDataKey", "kms:Decrypt" ], "Resource": "arn:aws:kms:REGION_NAME:ACCOUNT_ID:key/KEY_ID" }Replace
REGION_NAME,ACCOUNT_ID, andKEY_IDwith your values.
Credential character limitationsFor user credentials containing special characters, please avoid using the following characters:
@,[,],/,?,#,",\\,+, space,&,:as these characters can break connection string parsing.
- Click through to the Review step, choose a name for the policy, for example,
transfer-service-policy(this will be referenced in the next step), add a description, and click Create policy.
Create role
- Navigate to the IAM service page.
- Navigate to the Roles navigation tab, and click Create role.
- Select Custom trust policy and paste the provided trust policy (from the prerequisite) to allow AssumeRole access to this role. Click Next.
- Add the permissions policy created above, and click Next.
- Enter a Role name, for example,
transfer-role, and click Create role. - Once successfully created, search for the created role in the Roles list, click the role name, and make a note of the ARN value.
Alternative authentication method: AWS User with HMAC Access Key ID & Secret Access KeyRole based authentication is the preferred authentication mode for Redshift based on AWS recommendations, however, HMAC Access Key ID & Secret Access Key is an alternative authentication method that can be used if preferred.
- Navigate to the IAM service page.
- Navigate to the Users navigation tab, and click Add users.
- Enter a User name for the service, for example,
transfer-service, click Next. Under Select AWS access type, select the Access key - Programatic access option. Click Next: Permissions.- Click the Attach existing policies directly option, and search for the name of the policy created in the previous step. Select the policy, and click Next: Tags.
- Click Next: Review and click Create user.
- In the Success screen, record the Access key ID and the Secret access key.
Step 4: Add your destination
Use the following details to complete the connection setup: username, host, database, cluster, your chosen schema, IAM role ARN, and staging bucket details.
Permissions checklist
- Redshift database user exists and has
CREATEandTEMPORARYon the database. If you pre-created the schema, ensureGRANT ALL ON SCHEMA <schema> TO <username>. - IAM role trust policy allows data syncing service's to assume the role.
- IAM policy includes:
redshift:GetClusterCredentialson your target cluster (db user and db name resources).- S3
ListBucketonarn:aws:s3:::BUCKET_NAME. - S3
GetObject,PutObject,DeleteObjectonarn:aws:s3:::BUCKET_NAME/*.
- Network allowlisting (if enforced) permits egress IP/CIDR for the Redshift port (typically 5439).
FAQ
Q: How is the Redshift connection secured?
A: We use role-based authentication with your AWS IAM Role. The data syncing service's assumes your role to obtain short-lived database credentials and network access can be constrained by allowlisting the static egress IPs noted above.
Q: Why is an S3 bucket required?
A: Redshift's high-throughput path loads data from S3 using COPY. We stage files briefly in your bucket to maximize throughput and reliability. Files are cleaned up after load.
Q: What are the oaud vs sub IDs used for?
oaud vs sub IDs used for?A: These are identity claims used in the IAM trust policy when federating from GCP to AWS. sub uniquely identifies our Google principal in federation. oaud is an additional claim used to bind role assumption to your organization.
Q: Why am I getting authentication errors with Redshift?
A: Common causes:
- Missing or incorrect permission on
redshift:GetClusterCredentials(ensure it targets the correct cluster ARN and region/account). - Trust policy mismatch (the data syncing service's principal isn't permitted to assume your role).
- Using a Serverless workgroup permission or
redshift-serverless:GetCredentialsinstead of provisioned cluster +redshift:GetClusterCredentials. - Propagation delay: IAM changes can take a few minutes to apply. Retry after 5-10 minutes.
Q: Do I need to pre-create the schema?
A: No. The schema provided in the destination configuration is created automatically on first sync. If you pre-create it, grant ALL on the schema to the writer user and you may remove the database-level CREATE permission (retain TEMPORARY).
Updated 13 days ago